Today we will share the list of things you need to consider for Developing and implementing security controls for Azure Active Directory (Azure AD):
1. Identify Azure AD Assets:
- Create an inventory of all Azure AD assets, including user accounts, groups, applications, service principals, and Azure AD resources.
- Document the purpose and sensitivity level of each asset.
- Classify assets based on their importance and criticality to the organization, considering factors such as the data they provide access to or the applications they authenticate.
2. Perform a Risk Assessment:
- Identify potential threats to your Azure AD environment, such as unauthorized access, identity theft, insider threats, or data breaches.
- Assess vulnerabilities that could be exploited by conducting a comprehensive assessment of your Azure AD configuration and associated resources.
- Evaluate the potential impact of each threat and vulnerability on the confidentiality, integrity, and availability of your Azure AD assets.
- Determine the likelihood of each risk occurring based on historical data, industry trends, and the organization's threat landscape.
- Prioritize risks based on their potential impact and likelihood, focusing on those with the highest potential risk to your Azure AD environment.
3. Define Security Objectives:
- Review your organization's overall security strategy and compliance requirements, including any specific Azure AD security requirements.
- Identify specific security objectives that align with these requirements and the risk assessment findings. Ensure these objectives are measurable and relevant to your organization's needs.
- Examples of security objectives for Azure AD may include enforcing strong authentication policies, implementing conditional access controls, and protecting privileged accounts.
4. Select Security Controls:
- Research and review Azure AD security best practices, Azure Security Center recommendations, and Azure AD-specific security frameworks.
- Identify security controls available in Azure AD that address the identified risks and align with your security objectives.
- Examples of security controls for Azure AD include enabling multi-factor authentication (MFA), implementing conditional access policies, using Azure AD Privileged Identity Management (PIM), and leveraging Azure AD Identity Protection.
- Consider using Azure AD security features such as Azure AD Conditional Access, Azure AD Identity Governance, and Azure AD Privileged Identity Management to enhance your security posture.
5. Design Azure AD Security Architecture:
- Plan the structure of your Azure AD tenant, considering factors such as the number of Azure AD directories, users, groups, and applications required.
- Define the authentication and access models to be used, such as cloud-only identities, hybrid identities with Azure AD Connect, or federation with external identity providers.
- Determine the appropriate Azure AD license level and edition based on your organization's needs for advanced security features.
- Design RBAC roles and assignments for Azure AD resources, ensuring least privilege principles are followed.
- Establish Azure AD security policies, including password policies, sign-in risk policies, and device compliance policies.
6. Implement Security Controls:
- Enable multi-factor authentication (MFA) for Azure AD accounts, especially for privileged accounts and accounts with access to sensitive resources.
- Implement conditional access policies to enforce granular access controls based on user, device, location, and risk factors.
- Utilize Azure AD Identity Protection to detect and respond to suspicious sign-in activities and risky user behaviors.
- Leverage Azure AD Privileged Identity Management (PIM) to manage and monitor privileged access to Azure AD and other Azure resources.
- Regularly review and remediate risky sign-in events, risky users, and vulnerable configurations identified by Azure AD security features.
7. Provide User Training and Awareness:
- Develop training materials and conduct sessions to educate users about Azure AD security best practices.
- Train users on the importance of strong passwords, avoiding password reuse, and using MFA for enhanced security.
- Educate users about recognizing and reporting phishing attempts, suspicious sign-in activities, and other potential security risks.
- Raise awareness about the importance of safeguarding Azure AD credentials, avoiding sharing of accounts, and promptly reporting any unusual activities or potential security breaches.
8. Establish Incident Response Procedures:
- Develop an incident response plan specifically for Azure AD security incidents.
- Define roles and responsibilities for incident response team members, including those responsible for handling Azure AD security incidents.
- Establish communication protocols and reporting mechanisms to ensure prompt detection, response, and resolution of Azure AD security incidents.
- Document step-by-step procedures for isolating affected accounts, investigating potential breaches, resetting compromised credentials, and implementing necessary security measures to prevent future incidents.
- Conduct regular drills and exercises to test the effectiveness of the incident response procedures and identify areas for improvement.
9. Implement Monitoring and Auditing:
- Enable Azure AD auditing to track and monitor activities such as user sign-ins, application registrations, role assignments, and directory changes.
- Utilize Azure AD logs and Azure Monitor to collect and analyze security-related events and alerts.
- Configure alerts and notifications for suspicious activities, such as multiple failed sign-in attempts or privilege escalations.
- Integrate Azure AD with a Security Information and Event Management (SIEM) system for centralized log management, analysis, and correlation.
- Regularly review and analyze Azure AD logs and security reports to identify anomalies, detect security incidents, and take appropriate actions to mitigate risks.
10. Regular Assessment and Improvement:
- Continuously assess the effectiveness of your Azure AD security controls.
- Stay informed about Azure AD security updates, new security features, and best practices provided by Microsoft.
- Conduct periodic security assessments and penetration testing to identify vulnerabilities and weaknesses in your Azure AD environment.
- Monitor Azure Security Center recommendations and implement necessary security improvements.
- Regularly review and update your Azure AD security controls, policies, and procedures to adapt to emerging threats, industry standards, and regulatory requirements.
Certainly! Here's an expanded and elaborated checklist for developing and implementing security controls in Azure AD and AWS:
Checklist for Azure AD Security:
------------------------------------
| Step | Status
1 Identify Azure AD Assets
- List all Azure AD resources and services being used, such as users, groups, applications, and roles.
2 Perform a Risk Assessment
- Identify potential threats and vulnerabilities specific to Azure AD.
- Assess the impact and likelihood of each risk.
3 Define Security Objectives
- Clearly define and document the desired security objectives for Azure AD.
- Ensure objectives align with organizational requirements and compliance standards.
4 Select Security Controls
- Research and identify Azure AD-specific security controls provided by Microsoft.
- Choose controls that address identified risks and align with security objectives.
5 Design Azure AD Security Architecture
- Plan the structure of Azure AD, including directory structure and role assignments.
- Define secure connectivity options and network configurations.
- Establish data encryption strategies for Azure AD.
6 Implement Security Controls
- Enable multi-factor authentication (MFA) for Azure AD users.
- Configure strong password policies and password rotation requirements.
- Implement Azure AD Privileged Identity Management (PIM) for access management.
- Enable auditing and logging for Azure AD activities.
7 Provide User Training and Awareness
- Educate users about Azure AD security best practices and potential threats.
- Train users on recognizing and reporting security incidents or suspicious activities.
7 Establish Incident Response Procedures
- Develop an incident response plan specific to Azure AD security incidents.
- Define roles and responsibilities for incident response team members.
- Establish communication protocols and reporting mechanisms for incidents.
9 Implement Monitoring and Auditing
- Enable Azure AD auditing and configure logs for monitoring and analysis.
- Set up alerts and notifications for suspicious activities or policy violations.
- Integrate Azure AD logs with a centralized logging and monitoring system.
10 Regular Assessment and Improvement
- Conduct regular security assessments and vulnerability scans for Azure AD.
- Stay informed about Azure AD security updates and best practices.
- Continuously review and update Azure AD security controls and policies.
Remember that security is an ongoing process, and it's important to regularly evaluate and improve the security posture of your Azure AD environment to stay ahead of potential threats and ensure the protection of your organization's identity and access management infrastructure.
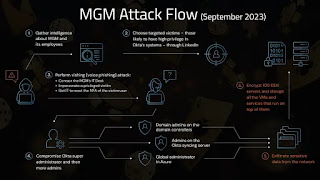
Finally here is an excellent blogpost by Mandiant for cloud platform compromise with multiple components that would require investigation
https://www.mandiant.com/resources/blog/cloud-bad-log-configurations