Social Engineering -
A single individual or groups of people attempting to gain access to your systems by utilizing the following methods.
Relies on interaction with humans, tricked into handing over credentials - humans are the weakest link therefore they try Deceptive techniques into breaking in.
Type of Social engineering Attacks :
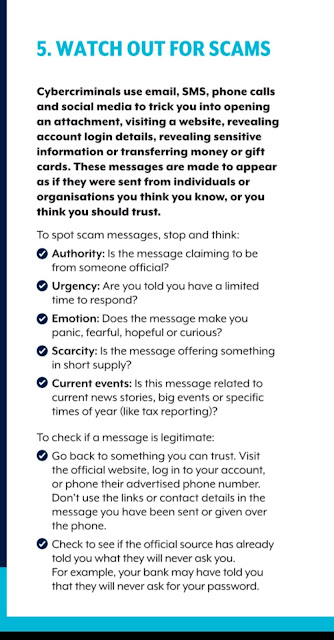
- Phishing - malicious email - sends a link
- Spear-phishing - targets individuals or specific groups
- Email spoofing - masquerading as someone else - appear as someone you think you know.
- Baiting - entice victim to do something, leave a usb lying around.
- Tailgating - gain access by following an employee through a door/gate.
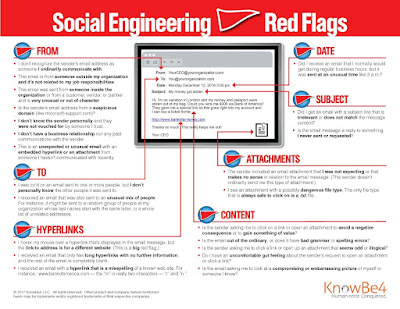
Indicator or Red Flags to look for investigation:
Email Sphere phishing: In this email fraud the perpetrator will ask for confidential and sensitive information. This type of attack resembles with e-mail spoofing fraud but in here in almost all cases the sender is someone trustworthy with an authoritative position in the organization.
Business email compromise is when criminals use email to abuse trust in business processes to scam organizations out of money or goods.
The Email forensic investigator can use several header fields to trace the email but it can be broadly categorized into the following area of interest the investigator should look into:
Sender's SMTP Server (OUTGOING Mail Server) >>
Encrypted mail header >>
Typical To, From, Subject, and Date Lines >>
Mail transfer email client information >>
Various X-header information added by different SMTP server and email clients during the whole email sending process.









0 comments:
Post a Comment